[translations idioma=”ES” url=”https://archives.rgnn.org/2013/10/22/reporteros-sin-fronteras-todo-el-mundo-deberia-preocuparse-por-la-seguridad-digital”]
WARSAW, POLAND. As part of the 13th World Summit of Nobel Peace Laureates in Warsaw, Reporters without Borders conducted a Civic Academy workshop on digital security.
Here is the result: an engaging presentation that ROOSTERGNN has complemented with an interview with Grégoire Pouget from the RWB’s New Media Desk. (Information taken from the presentation is highlighted in italics below).
ROOSTERGNN: Who should care about digital security? Why should journalists in particular take extra care?
Grégoire Pouget: Everyone should care about digital security. Journalists should take extra care because their whole work is about information and nowadays, a lot of information is found, exchanged and sent over the Internet. Journalists have to protect their sources, their contacts, their colleagues and themselves. They must know how easy it is to intercept and read an email and they have to know how to prevent themselves from this kind of threat. Email is just an example amongst many others (Skype, chat services, etc.).
To repeat the words of Christopher Soghoian:
“BRAVE journalists have defied court orders and have even been jailed rather than compromise their ethical duty to protect sources. But as governments increasingly record their citizens’ every communication — even wiretapping journalists and searching their computers — the safety of anonymous sources will depend not only on journalists’ ethics, but on their computer skills.”
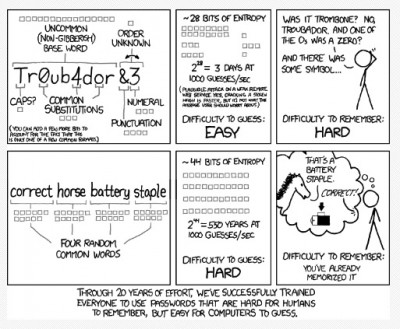
Specifically, the RWB presentation asks users “How secure is your password? Who wants to try?”
Instead, it is recommended that you use Passphrases.
Never use the same passphrase twice. If you need some help, use password managers such as lastpass or onepassword.
There are many traces left on your computer that can lead to your data: browsing history, cookies, stored passwords, file history, chat logs, emails, apps history, etc.
Solutions
- Use private browsing
- Check your privacy options, secure delete your files
- Even better: use a live OS, such as Tails.
ROOSTERGNN: How can you switch to private browsing? When you say one should secure delete one’s files how does one do that exactly?
Grégoire Pouget: In Firefox: go in the file menu then select “New private window”. Keyboard shortcut : Ctrl + Shift + P
In chrome: go in the file menu then select “New incognito window”. Keyboard shortcut : Ctrl + Shift +
To secure delete files on Mac OS X : Command + Right click on the trash then select “Secure empty trash”
To secure delete files on windows, install the Eraser software.
To avoid interception, use:
- https: encrypts your web browsing when available on the visited website
- Tor bundle: anonymise your web browsing. Anonymisation is NOT encryption
- VPN: encrypts every network connection coming from your device
ROOSTERGNN: What email service do you recommend?
Grégoire Pouget: It depends. You can use riseup.net, an email service maintained and run by hacktivists. Riseup will do everything they can to protect your data. But using this kind of service puts a red flag “I use a service maintained by hacktivists” on your emails.
You can then use a Gmail or Yahoo account because there are so many people using those services that your emails get lost in the crowd. But you have to know that yahoo or Google might collaborate with the US government. And you know for sure that if they have a request form a judge, they have to fulfill it.
The best email service to use depends on your threat model. If you think the US government may be interested by your emails, don’t use Gmail or Yahoo or any email provider located in the US. Use rather an email provider located in your country, in Sweden, etc. Try to avoid any “free” email provider. On the Internet, if you’re not paying for [something], you are the product. Paying for your email can be a guarantee that your emails are protected. The best solution, for those who can, is to run your own email server. But this is not realistic.
A smartphone is a computer. Everything already mentionned is also true for a spyphone smartphone. Use a dumbphone instead. Or have a look at the Guardian Project, Redphone, Silence Circle, etc.
Active communication
- Lawful interception
- GSM is not very much secured. Rainbow table + a bit of radio hardware = encryption cracked for less than $500.
ROOSTERGNN: When is data interception legal?
Grégoire Pouget: It depends on the countries, it depends on the law. Usually a judge must be involved. But not always. For instance, the FISA Act in the US has allowed the NSA to monitor email and phone call without any search warrant.
Device in standby mode
A lot of softwares can turn a cellphone into a microphone bug. However, it has to be installed on the cellphone.
Device off
The battery is still providing power to the cell phone. With the help of the telephone operator, who can access the Application Protocol Data Unit (packets sent to the SIM card), it can still be activated.
Battery removed
No battery, no power, no signal, no spying.
In my fridge ← Snowden
Note : you can’t remove your iPhone battery
ROOSTERGNN: When you say that the iPhone battery cannot be taken out, does that mean users can be tracked even though their phone is off?
Grégoire Pouget: When your battery is still in your cellphone, you can’t be sure that you are not spied on. Your cellphone can have been the target of a specific malware that could allow someone to remotely turn on the microphone. If you are targeted by a government, and if your operator is wiling to collaborate, your operator is able to access the Application Protocol Data Unit (packets sent to the SIM card) and to activate it. It’s not a certainty but just a possibility. If you want to be sure your phone won’t be used to spy on you, remove the battery.
ROOSTERGNN: There appear to be more and more steps to be taken to protect one’s privacy. Where does one draw the line? How much is enough?
Grégoire Pouget: As mentioned above, everything depends on your threat model. What is the topic you’re working on, who may be interested by your information… If you are a former NSA analyst and you are releasing documents to some journalist located in Brazil, you’ll have to be extremely cautious and nothing may be enough.
If you are a citizen who thinks his personal information should remain private, there are some easy steps you can take to protect your privacy.
Security, whether it is about sources protection or privacy protection, is a process. Depending on the amount of information you have to protect and from whom you have to protect it, the process length may vary.
Follow the World Summit of Nobel Peace Laureates series here.